IF YOU’RE GOING TO BE PROTESTING or in any sort of situation where there’s a higher-than-average chance of having potentially adversarial encounters with the police, and if you have an iPhone, please remember these two tips:
- Memorize how to quickly “hard lock” your phone. It’s easy to do, even as you’re pulling your phone out of your pocket or bag: hold the power button and either volume button for about two seconds. Your screen will flip to show the “slide to power off” toggle, along with the Medical ID and emergency call toggles. Once you’ve done this, Face ID/Touch ID is disabled, and you must enter your passcode to unlock the phone. (If you keep holding the buttons for five or more seconds, your phone will automatically call emergency services.)
While there are some legal disputes over this, currently the police cannot force you to surrender your phone passcode, but they might be allowed to force you to use Touch ID/Face ID to unlock it. By hard locking your phone, you’re locking them out until/unless they get a warrant. If the police ever ask you to surrender your phone, hard lock it as you hand it to them.
I also recommend switching from a standard 4- or 6-digit passcode to a longer, alphanumeric password. To set this up, go to Settings > Touch ID/Face ID & Passcode, tap Turn Passcode On, and tap Passcode Options and set your passcode. This is much more secure than a short numerical passcode, and if your phone ever gets confiscated, will make it much more difficult for authorities to gain access to your phone.
-
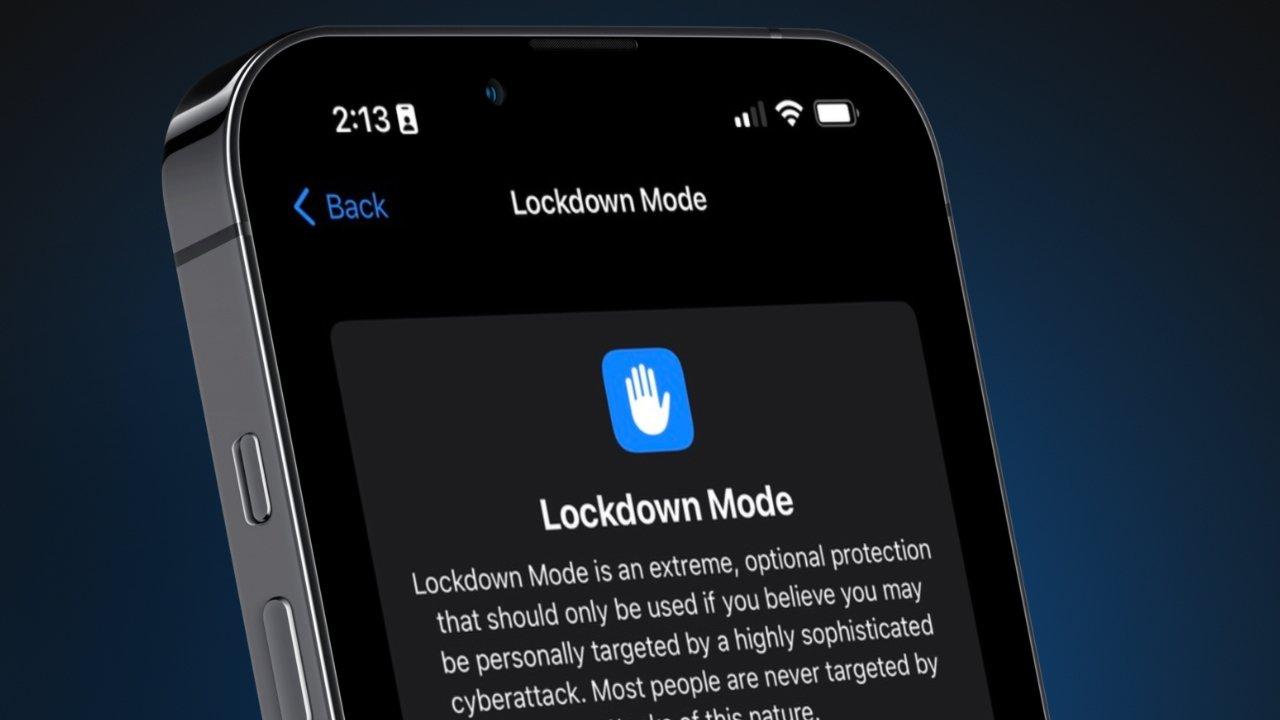
Either before you join the protest, or if you see the police presence start to ramp up, TURN ON LOCKDOWN MODE.
Settings > Privacy & Security > Lockdown Mode > On
Note: This is not a setting that most people need to have enabled full-time. It’s designed, in Apple’s words, “for the very few individuals who, because of who they are or what they do, might be personally targeted by some of the most sophisticated digital threats.” Turning it on will severely restrict how your phone works in a number of ways (see Apple’s Lockdown Mode support document for details). However, it also makes it much more difficult for anyone to track you, intercept your communications, or otherwise gain access to your phone.
Make your voices heard! But keep yourself safe as you do.
Android users will have to do their own research for these or similar techniques. Or get better phones. ;) (Yes, I’m kidding. Use what works for you.)
(Image yoinked from AppleInsider’s Lockdown Mode post until I can make my own.)